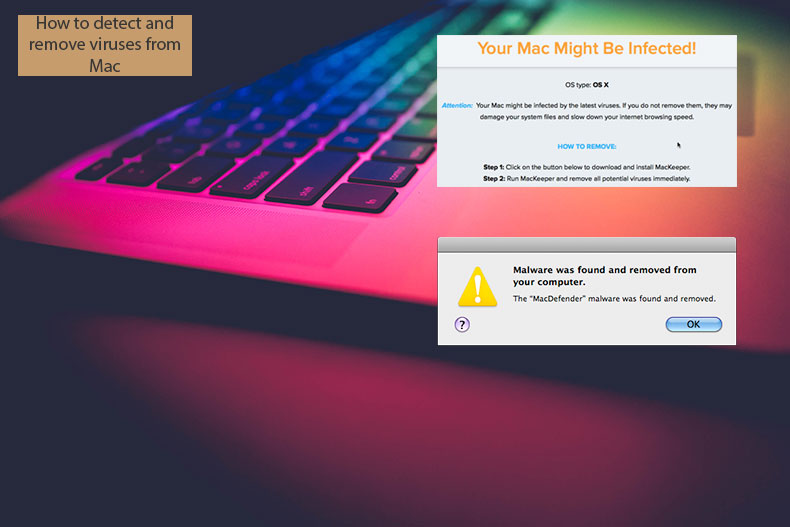
How to Detect and Remove Viruses on Mac?

(updated)
Get Free Scanner and check your computer for errors
Fix It NowTo fix found issues, you have to purchase the full version of Combo Cleaner. Free trial available. Combo Cleaner is owned and operated by Rcs Lt, the parent company of PCRisk.com read more.
Think Your Mac is Infected? How to Detect and Remove Viruses and Malware on Mac Computers?
Many Mac computer users believe that Apple computers are perfectly protected from any type of malicious software or virus code. This situation might have been true for some considerable time. However, the prevalence of malware has increased with the growing popularity of Apple products.
On the other hand, mobile devices such as iPhone, iPad, and iPod touch remain relatively safe since most malicious software and viruses are developed to infect the macOS operating system. Despite this, some of these infections transfer from Macs to iOS devices connected via a USB cable.
As compared to the Windows operating system, the Mac operating system includes an increasingly effective protection system. System updates are delivered with a new version of a database, including known malware and viruses. This allows computers to search and block these infections automatically.
This article describes common causes of computer infections, how the system behaves in response to them, and how to diagnose existing threats.
Video showing How to Clear Mac From Viruses and Malware?
Table of Contents:
- Introduction
- What is the difference between viruses and malware?
- Most common signs of an infected computer
- Most common methods how your computer gets infected
- Built-in protection tools
- Use Combo Cleaner to clear your Mac
- Recommended actions when Mac is infected
- Video showing How to Clear Mac From Viruses and Malware?
Download Computer Malware Repair Tool
It is recommended to run a free scan with Combo Cleaner - a tool to detect viruses and malware on your device. You will need to purchase the full version to remove infections. Free trial available. Combo Cleaner is owned and operated by Rcs Lt, the parent company of PCRisk.com read more.
What is the difference between a virus and malware?
First, we will clarify the definitions of malware and a virus. Malicious software (malware) usually behaves like various applications and often appears to do little when opened. In fact, these applications add extra applications that might display pop-up ads and change the home page and default search engine settings.
These infections are mainly used to display advertisements; however, they sometimes also track browsing history, most used queries, etc. Viruses are small portions of computer code designed to go unnoticed. However, they often reduce Mac performance. Checking the activity monitor will enable you to see the kernel task consuming extensive computer resources due to the prevalence of a virus since it is designed to protect the Mac from overheating.
Most common signs of an infected computer
There are many symptoms of Mac infection, but these might vary with the type of software installed on your computer. Here we describe the most common scenarios to alert you of the need to check for malicious software.
Computer performance has noticeably decreased. It becomes sluggish, and the activity monitor displays various mysterious processes running in the background, consuming Mac resources.
You notice a new toolbar on the web browser that you have not intentionally installed. In most cases, these toolbars encourage you to shop or search faster by typing a search query directly into the toolbar.
Casual Internet browsing loads unexpected results or redirects to irrelevant websites. Search queries appear within an unfamiliar search engine.
Websites you open display many advertisements, including those that should be ad-free (for example, Wikipedia).
Your favorite websites (that you usually visit daily) do not load, or you are randomly redirected to advertising web pages.
Advertising windows continually pop up on the desktop, and you cannot find any association with websites you browse or programs you run.
If you have noticed any of these symptoms, do not panic - performance is often reduced for several reasons, and it may not result from a virus or malware on the system. Additionally, some developers attach ads to their software to introduce you to their other products. Nevertheless, it is always safer to scan your computer for possible threats.
Bear in mind, however, that if you simply enter a query describing your problem and download the result, it might be malware or a fake application.
Most common methods of computer infection
Knowing how malware and viruses infect your computer will help you to diagnose or prevent possible threats. The methods vary with the type of threat. However, there are many common ways that unwanted software can infiltrate your computer. Check the list below to ensure that the threats have not infiltrated your Mac.
Malicious software
As mentioned above, malware and malicious software are merely synonyms for a typed threat introduced as 'free' (or sometimes paid) software that supposedly cleans or protects your computer from viruses. This software appears when the search query contains keywords about fast, easy, and free viruses removal in the most frequent cases.
To avoid these threats from malicious software, check independent reviews of applications or ask for personal recommendations from other users. These threats are spread by downloads, emails, or even instant messages.
Fake files
Malicious software and viruses are frequently hidden within common files, such as images and Word or PDF documents. Many computer users know the dangers of opening executable files such as .dmg on Mac computers and .exe on Windows. Still, few believe that simple image or document files might also contain threats.
The best precaution is to open files from trusted or known sources only and avoid opening data that appears on your desktop randomly or together with the installation of untrusted software.
Fake updates or system tools
Another popular and confusing method used to spread malware is through various pop-up dialog boxes. These encourage you to upgrade your software and apply additional tools to access the content. The Adobe Flash Player browser plug-in is a popular way to hide threats within its installation files. We strongly recommend that you add and update this plug-in through their official website only.
Randomly contacted by 'technical help'
Occasionally, users receive calls from people claiming to be Apple or Microsoft 'technicians'. They often state that your computer is likely to be infected and you should follow some steps to clean it. Following their guidance will add malicious software to your system.
Built-in protection tools
With system updates, Apple includes tools that work in the background to protect users from malware and viruses. You are advised to check how they are invoked and what actions they perform.
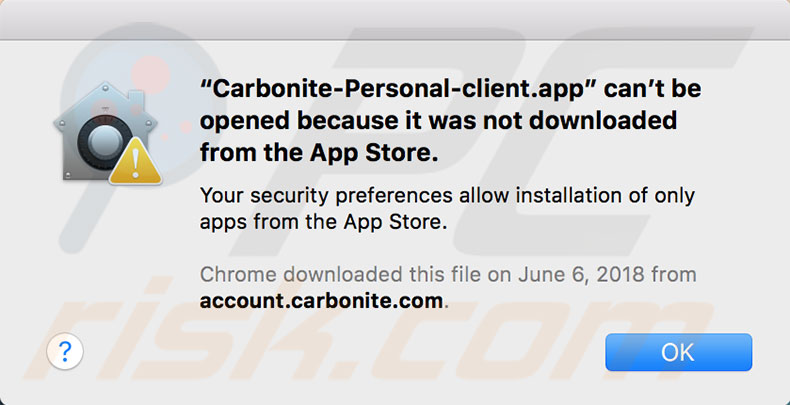
File Quarantine or Gatekeeper
Most Mac users are familiar with this tool, but not all know how it is invoked and what function it actually performs. When attempting to open an application you have downloaded or installed from external storage, you will see a warning message that displays information about the source from which it was downloaded.
You must manually choose to open the file unless the application is downloaded from Mac App Store since these apps are acquired from a trusted Apple source. Suppose you are trying to launch an application that was not digitally signed by the developer (a condition enforced by Apple). In that case, the File Quarantine/Gatekeeper tool will block access to this particular application.
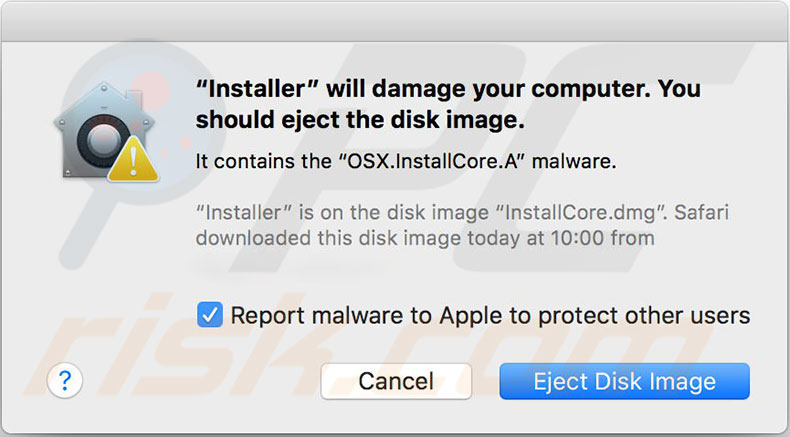
Xprotect
This tool contains a slightly more aggressive prevention policy against files recognized as possible malware or virus infections. When trying to open files for the first time after download, this tool checks the entire package and compares it with the database of known malware or viruses. If it finds any matches, you will see a message stating that files are infected or damaged, and the only option offered is to move the file to the trash.
The Xprotect tool works very successfully and is one of the main reasons infected Mac computers are rare. This tool might sometimes block older versions of legitimate software, such as Java or Flash plug-in since it was proven that these plug-ins are vulnerable to malware attacks.
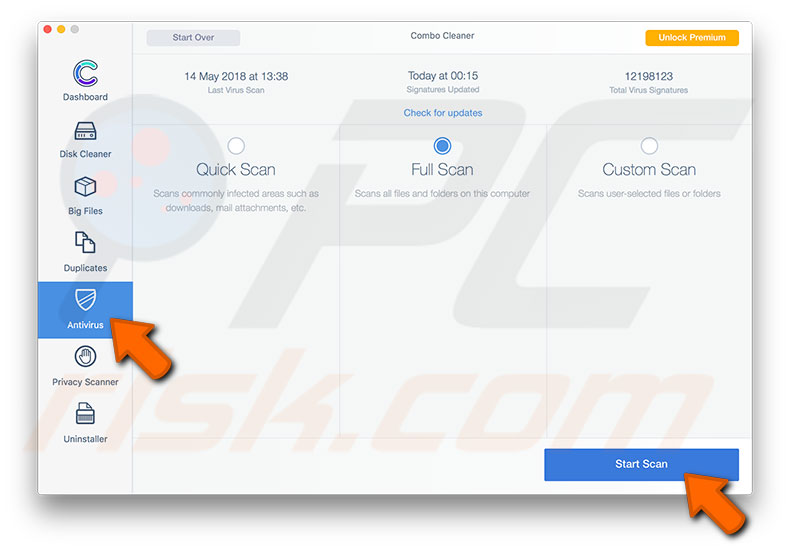
Use Combo Cleaner to clear your Mac
Combo Cleaner contains two virus scan engines. The first checks for Mac-based malware infections during the second search for PC generic security threats. This software scans the Mac and also checks web browsers for potentially unwanted plug-ins and infected emails. Although infected emails do not directly cause system problems, this option prevents possible threats spread via email messages.
First, visit the Combo Cleaner developers website, and get the software. Then, launch it and select Antivirus in the left side panel. Choose Quick Scan, Full Scan, or Custom Scan. Quick Scan is the best option when you suspect that you might have threats on your computer but do not have time to perform a full scan.
Full Scan will scan all files stored within the Mac hard disk. This option might take some time, depending on the number of files your storage area contains. A Custom Scan might be the best option when you wish to check specific files or folders.
Recommended actions when Mac is infected
Following the steps below, you can decrease the risk of problems caused by malicious software. Also, you will be able to eliminate threats to the Mac.
Avoid entering passwords
If you suspect that your computer might be infected by a virus or malware, do not enter any passwords or login details due to the possibility of a hidden keylogger running in the background. This software is commonly deployed with malware and viruses. Bear in mind that some of these infections record periodical screenshots, so you should avoid revealing any passwords when copying and pasting from a document or clicking the Show password option.
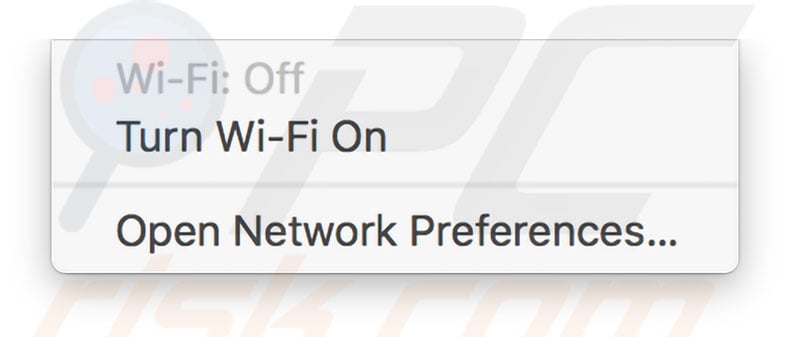
Stay offline
Another good precaution is to disconnect from the Internet. Turn off the Wi-Fi and/or unplug the Ethernet cable from your computer until you are sure the computer is safe. This will protect your private data from any third parties since most malware data is sent to the servers, where developers can access it.
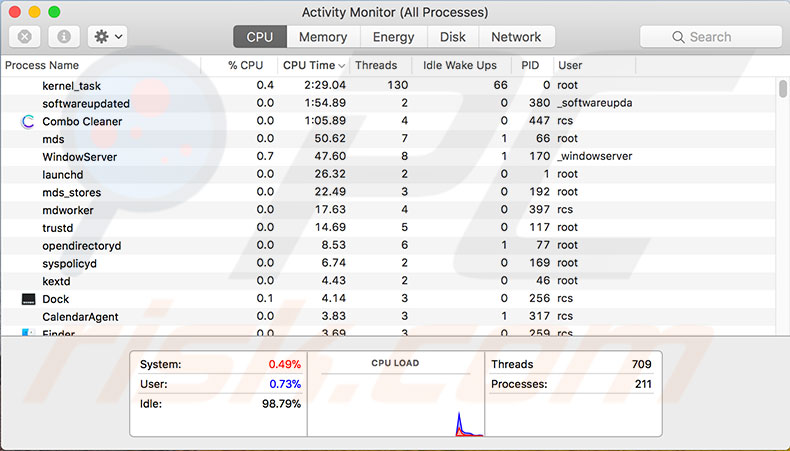
Activity Monitor
If the information above helped you consider recent files you have downloaded or installed to your computer, try to remember their names.
1. If the application is running, turn it off using the keyboard shortcut of Command and Q or simply click the Quit button in the top left corner of the window.
2. Further, open Activity Monitor by using Spotlight or going to Applications and then the Utilities folder through Finder.
3. Once Activity Monitor is launched, locate the search field at the top right corner of the window and type the name of the malicious software. Often, you will find that the application is still running in the background, even though you have closed it recently.
4. Select the running app, click the X icon at the top left of the toolbar, and click Force quit.
Most malware developers are aware of this situation and thus deliver random, unused names to make it difficult to find the particular process.
Shut down and restore
1. If possible, turn off your computer and enter Recovery Mode by holding down the Command and R keys while pressing the power button - hold down these keys until you see the Apple logo.
2. Restore your Mac from a recent backup, such as Time Machine or another application. Remember that you should select the backup created before the point at which you believe the Mac was infected.
3. When the restore process finishes and your computer is rebooting, ensure that external storage is not connected to the Mac (if it previously had contact with the infected device). Also, be vigilant and do not open fake applications, emails, or files that contain threats.
The best option is to connect external storage to a Windows computer running antivirus software (although the infection is based on a Mac operating system, these programs should detect and remove it).
Protect credit card details
If you think your computer was infected with one of the above methods, delete the files immediately. If, however, you have made any transfers or purchases from your credit card, especially for software that appeared to be fake, contact your credit card company or bank immediately and explain the situation to ensure that your credentials are not used elsewhere. You might receive refunds for bogus money transfers.
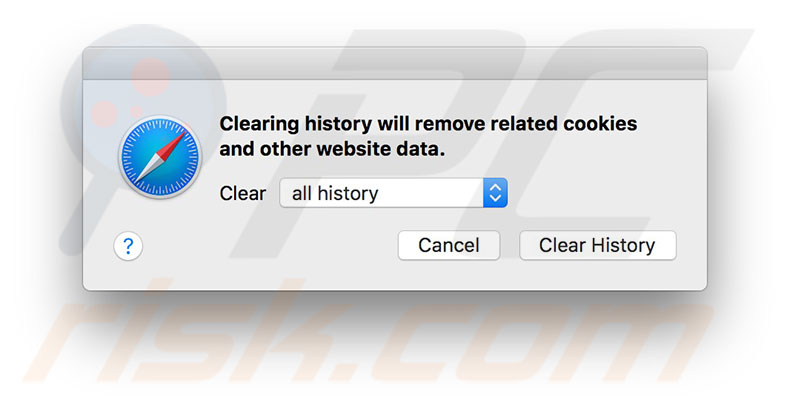
Clear junk files
To ensure you have eliminated the infection completely, also clear all the junk files. Clear the Internet browser cache manually.
1. Open Safari and click on Safari in the menu bar at the top of your screen, then select Clear History.
2. In the new pop-up window, choose all history of the drop-down list, and finally click Clear History.
3. Next, delete the entire download folder. Open this folder through Finder, select all files, drag to Trash, or right-click and select Move to Trash.
4. Finally, open Trash and select the Empty the Trash option.
Change passwords
A final option is to secure all logins. Once you are sure the computer is completely clear of infections, change all passwords, including websites, cloud services, applications, etc. You are advised to contact your credit card company or bank to notify them of the current situation - they might then heighten attention for attempts to access your account in the future.
Reinstall macOS
If you have endured many unsuccessful attempts to clean the Mac, there is another option that will work in most cases: consider a complete reinstallation of the Mac operating system. Detailed instructions are in this guide.
Share:

Karolina Peistariene
Author of how-to guides for Mac users
Responsible for collecting, analyzing, and presenting problem-solving solution articles related to macOS issues. Years of macOS experience combined with solid research and analyzing skills help Karolina provide readers with working and helpful solutions as well as introduce various features Mac has to offer.
▼ Show Discussion