'COMPUTER HEALTH IS CRITICAL' Error
Also Known As: PUPs causing fake error messages
COMPUTER HEALTH IS CRITICAL removal instructions
What is COMPUTER HEALTH IS CRITICAL message?
This false error message pops-up when the system is infected with adware-type applications such as Games Desktop, MovieDea, and Desktop-play. All claim to provide various useful features that supposedly improve the Internet browsing experience, however, fake promises delivered by adware-type apps are simply attempts to trick users to install. Rather than providing the functionality promised, these applications gather personal data, deliver intrusive online advertisements, and generate this fake error message.
The message states that the system encountered an error and the computer has been stopped to prevent damage and data loss. Users are then encouraged to contact a 'Microsoft Certified Technician' via the telephone number provided (1-855-210-6024). This information is false. You should ignore the error message and eliminate the potentially unwanted program (PUP) responsible for its generation. Display of error messages is uncommon behavior for adware. Error messages offering help, and then encouraging users to contact technicians, are often generated by ransomware-type applications. Never follow these guidelines - you will risk being scammed.
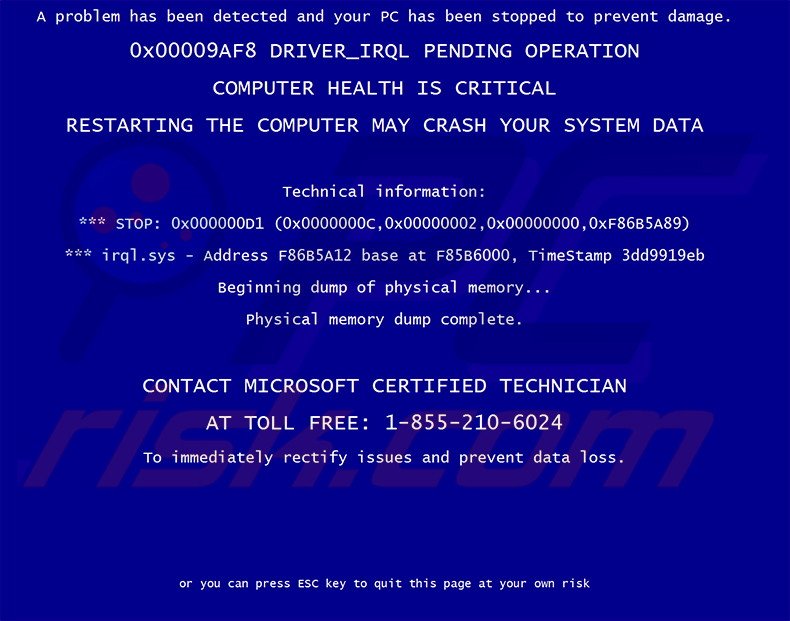
Text presented by this fake error message:
A problem has been detected and you PC has been stopped to prevent damage.
0x0009AF8 DRIVER_IRQL PENDING OPERATION
COMPUTER HEALTH IS CRITICAL
RESTARTING THE COMPUTER MAY CRASH YOU SYSTEM DATA
Technical information:
***STOP: 0x00000D1 (0x000000c, 0x0000002, 0x00000000, 0xF86B5A89)
*** irql.sys - Address F86B5A12 base at F85B6000, TimeStamp 3dd9919eb
Beginning dump of physical memory…
Physical memory dump complete.
CONTACT MICROSOFT CERTIFIED TECHNICIAN
AT TOLL FREE: 1-855-210-6024
To immediately rectify issues and prevent data loss or you can press ESC key to quit this page at your own risk.
Applications that generate this error message are similar to other adware-type apps including, for example, Safe Browsing, Steel Cut, DesktopClock, and Sidebar Dock. These offer useful features, however, they simply display intrusive online advertisements and collect personally identifiable information. Adware-type applications are designed solely to generate revenue for the developers and provide none of the functionality promised.
How did adware install on my computer?
Applications such as these are commonly distributed using a deceptive software marketing method called 'bundling' (stealth installation of PUPs with the chosen software/apps), and thus, usually infiltrate systems without users' permission. Research shows that many users do not express enough caution when downloading and installing software - they simply rush these processes and skip most/all steps. Aware of this, developers conceal PUPs within the 'Custom' or 'Advanced' settings. By skipping this section, users often install deceptive applications inadvertently and expose their systems to risk of infection. The developers are concerned only with the amount of revenue generated, and thus, do not properly disclose installation of PUPs (inluding the ones generating this fake error message).
How to avoid installation of potentially unwanted applications?
There are two simple steps you should take to protect your system from adware infections. Firstly, pay close attention when downloading and installing software - select the 'Custom' or 'Advanced' settings and follow all steps (since rogue applications are usually hidden). Secondly, never accept offers to install additional programs. Adware-type applications are often distributed in groups, and therefore, you should opt-out of additional third party applications.
Quick menu:
- What is COMPUTER HEALTH IS CRITICAL?
- STEP 1. Uninstall adware-type applications using Control Panel.
- STEP 2. Remove adware from Internet Explorer.
- STEP 3. Remove delusive plug-ins from Google Chrome.
- STEP 4. Remove dubious add-ons from Mozilla Firefox.
Adware removal:
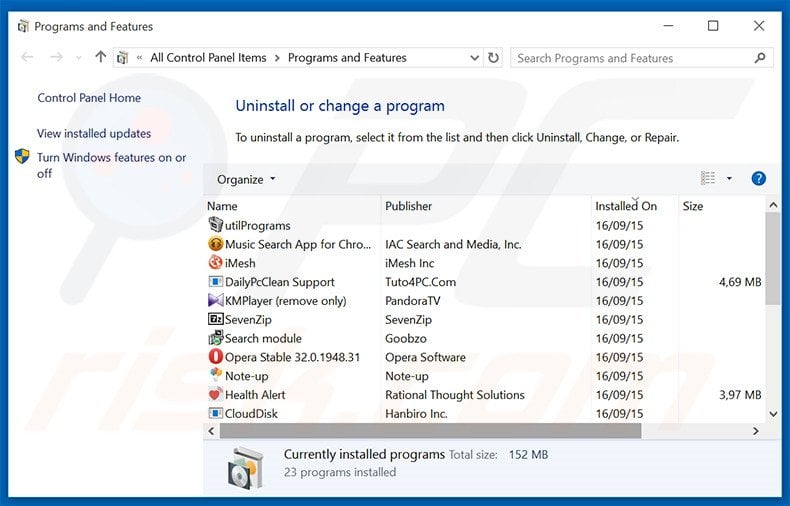
In the uninstall programs window, look for any recently-installed suspicious programs, select such entries and click "Uninstall" or "Remove".
After uninstalling the potentially unwanted program that causes COMPUTER HEALTH IS CRITICAL error message, scan your computer for any remaining unwanted components or possible malware infections. To scan your computer, use recommended malware removal software.
Remove adware from Internet browsers:
Video showing how to remove potentially unwanted browser add-ons:
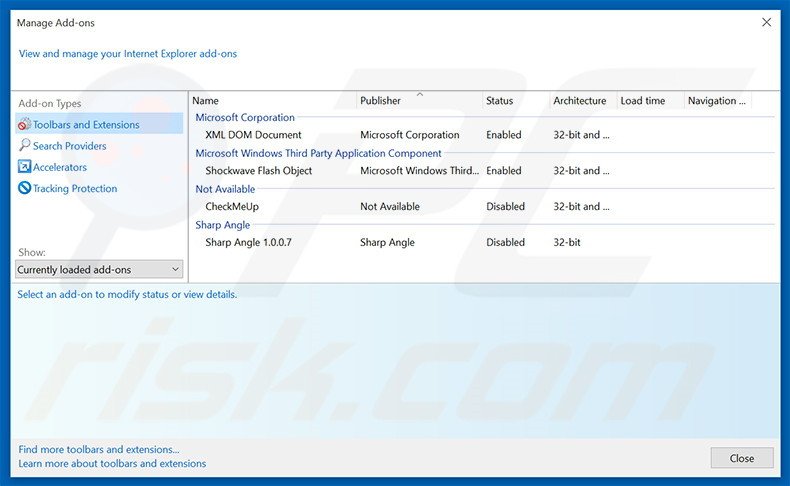
 Remove malicious add-ons from Internet Explorer:
Remove malicious add-ons from Internet Explorer:
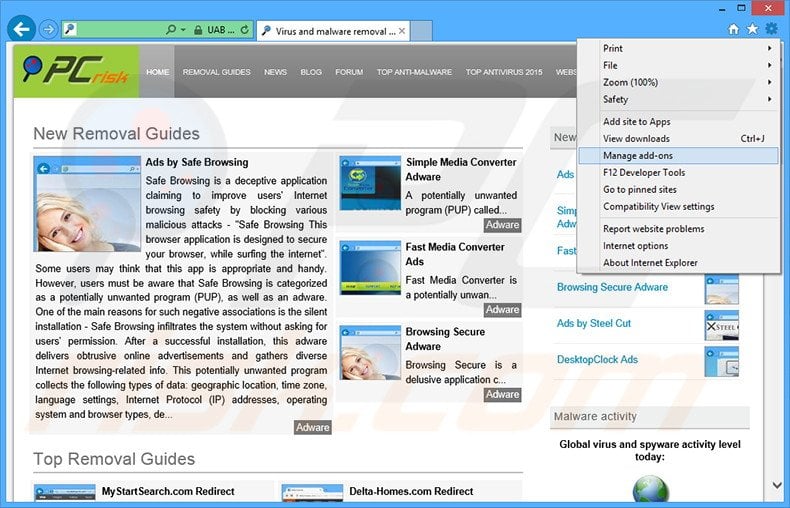
Click the "gear" icon ![]() (at the top right corner of Internet Explorer), select "Manage Add-ons". Look for any recently-installed suspicious browser extensions, select these entries and click "Remove".
(at the top right corner of Internet Explorer), select "Manage Add-ons". Look for any recently-installed suspicious browser extensions, select these entries and click "Remove".
 Remove malicious extensions from Google Chrome:
Remove malicious extensions from Google Chrome:
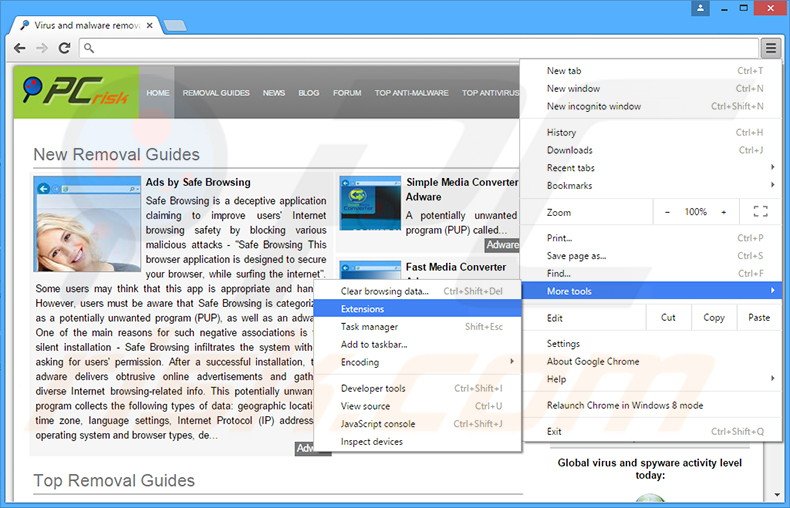
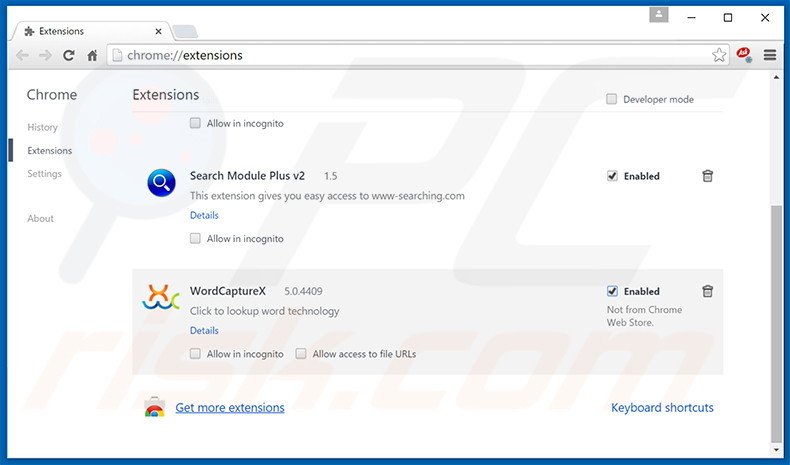
Click the Chrome menu icon ![]() (at the top right corner of Google Chrome), select "Tools" and click "Extensions". Locate all recently-installed suspicious browser add-ons, select these entries and click the trash can icon.
(at the top right corner of Google Chrome), select "Tools" and click "Extensions". Locate all recently-installed suspicious browser add-ons, select these entries and click the trash can icon.
 Remove malicious plug-ins from Mozilla Firefox:
Remove malicious plug-ins from Mozilla Firefox:
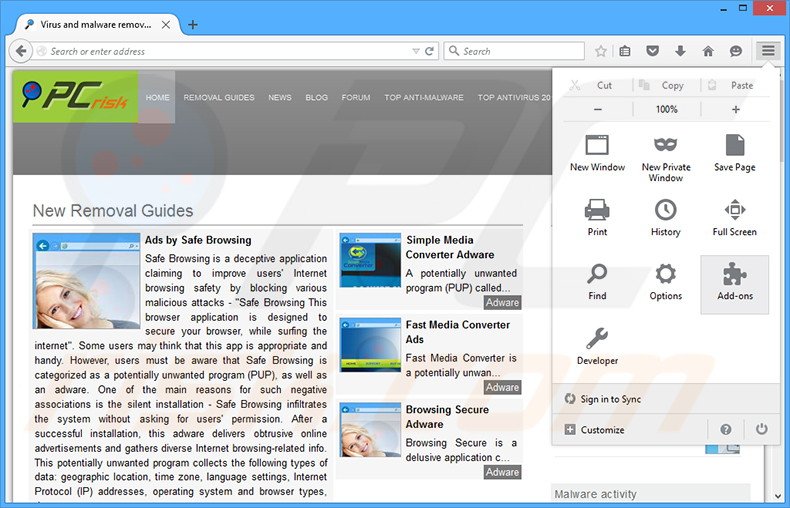
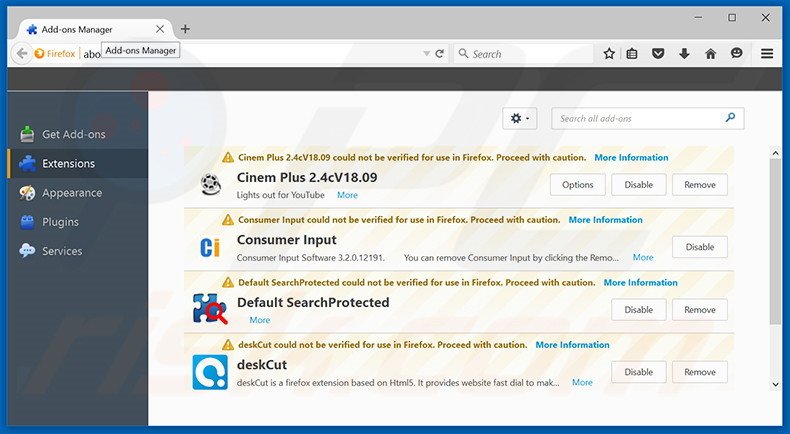
Click the Firefox menu ![]() (at the top right corner of the main window), select "Add-ons". Click "Extensions", in the opened window, remove all recently-installed suspicious browser plug-ins.
(at the top right corner of the main window), select "Add-ons". Click "Extensions", in the opened window, remove all recently-installed suspicious browser plug-ins.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.

▼ Show Discussion