What Is a Fake Antivirus and How to Tell if It’s Fake?
Rogue programs, fake antiviruses, fake security scans, fake antispyware, etc., are some of the most prevalent infections today. When encountering many of the above software packages, most users believe they are genuine security products that do a good job. And of course, most of those users go on to enter their credit card details to 'purchase' one of these antivirus programs. Unfortunately, there is a high probability that the user is then charged considerably more than the price declared in the shopping cart.
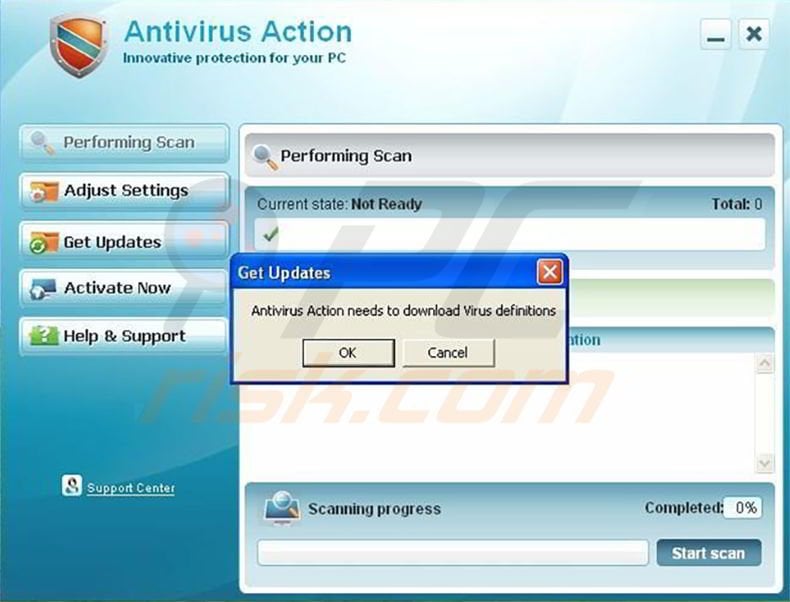
Over time, these rogue antivirus and antispyware programs have gained an increasingly professional appearance. Many even attempt to imitate the interface of legitimate antivirus or antispyware products. These programs are often derived from families so that an identical program may adopt many names. For example, 'Windows Recovery,' 'Windows XP Recovery,' 'Windows Diagnostic,' 'Windows Vista Recovery' are names representing a single rogue program.
How to Know if a Security Program Is Fake?
Here are the main symptoms of typical fake security programs:
- The program appeared on your system without your knowledge. You didn't willingly download or install it, but somehow the program is now scanning your computer for viruses and spyware and advises you to take certain actions.
- You cannot close it, shut it down, or uninstall it.
- It appears to run various scans and 'detects' a group of infected files on your computer. It generates error messages suggesting that your data is at risk and you must clean your computer immediately. It attempts to scare and intimidate the user in every way possible.
- The complete computer scan takes just a few minutes. Genuine antivirus or antispyware software requires considerably more time to scan your entire hard disk.
- The fake antivirus or antispyware software's primary purpose is to scare users into purchasing the program by offering to fix the 'errors' supposedly detected.
If the behavior of the program in question does not meet any of the symptoms mentioned above, carry out further research by carrying out an Internet search on the name of the product. Typically, searching the program name will help to verify its authenticity. If most search results offer ways to remove this program from your system, you can be sure that this program is a scam.
How to Protect Your Computer?
- Be careful of infections originating from video codecs. For example, if you see a link on the social network to a video with a statement such as, "Watch this, you will be surprised very very much!", you are likely to be asked to install codecs or an Adobe Flash Player update. In most cases, this will be a virus, spyware, or rogue program, so do not follow the instructions.
- If you receive an email from an institution (usually a well-known company), and the email contains general information without your name, be cautious since these emails often encourage you to open infected attachments. You can scan the attachment with updated antivirus and antispyware programs or choose not to open it at all until you can verify the letter's authenticity.
Remember, if you do not use antivirus or antispyware software, the possibility of your computer becoming infected increases significantly.
Share:

Tomas Meskauskas
Expert security researcher, professional malware analyst
I am passionate about computer security and technology. I have an experience of over 10 years working in various companies related to computer technical issue solving and Internet security. I have been working as an author and editor for pcrisk.com since 2010. Follow me on Twitter and LinkedIn to stay informed about the latest online security threats.

▼ Show Discussion